Military contractors are usually poised at the cutting edge of DOD cybersecurity programs. Their contributions help the US maintain the most impressive standing army in the world. Because of their position, they have always needed to have top-notch cybersecurity.
Before now, the US Government hasn’t had to put guidelines in place to enforce robust cybersecurity. That changed in June 2020, with the Cyber Security Maturity Model Certification (CMMC). According to the Office of the Under Secretary of Defense for Acquisition and Sustainment (OUSD(A&S)), the CMMC combined several security standards and industry best practices to reduce the risk of threats to contractor systems.
The implementation of this certification has changed the way contractors do business. In this article, we’ll look at the measures that the DOD has implemented to ensure governmental data safety when working with contractors. We’ll also delve into how contractors can figure out if they comply with current standards.
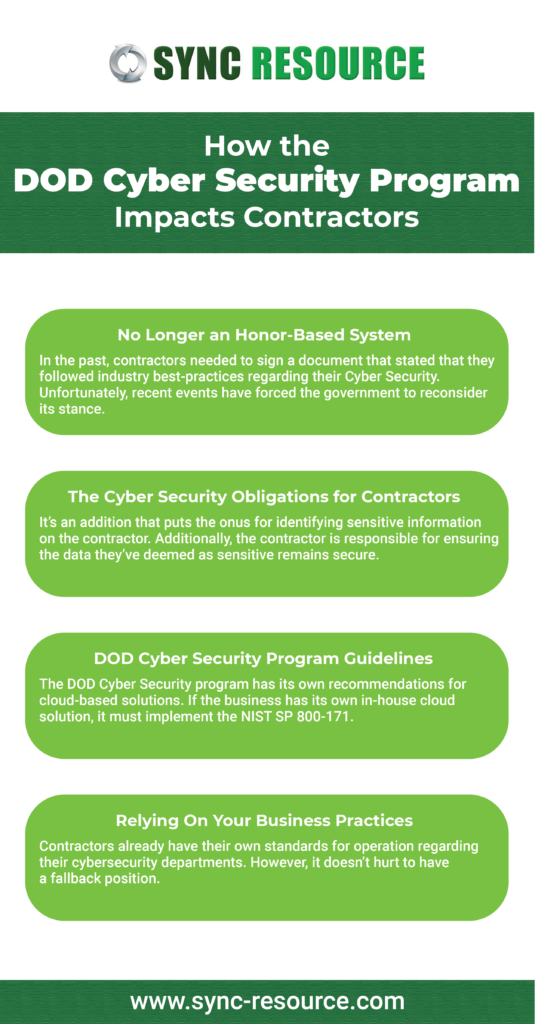
No Longer an Honor-Based System
In the past, contractors needed to sign a document that stated that they followed industry best-practices regarding their Cyber Security. Unfortunately, recent events have forced the government to reconsider its stance. In March 2019, NBC News reported that Iranian-backed hackers gained access to contractor systems, acquiring sensitive data on government-funded projects. Because of the potential fallout associated with sensitive information, the Pentagon decided to take action. The CMMC resulted from consultation, which was designed to ensure that contractors complied with the security standards the government has come to expect from its contractors.
The Cyber Security Obligations for Contractors
The DOD Cyber Security program focuses on one specific clause. The Defense Federal Acquisition Regulation Supplement (“DFARS”) clause 252.204-70122, also known as the “7012 clause.” It has also been referred to as the Safeguarding Covered Defense Information and Cyber Incident Reporting clause. It’s an addition that puts the onus for identifying sensitive information on the contractor. Additionally, the contractor is responsible for ensuring the data they’ve deemed as sensitive remains secure.
Contractors need to be aware of the information they will receive. Typically, the 7012 clause deals with “covered defense information” (CDI). CDIs include unclassified controlled technical data and any information inside the controlled classified information registry. If interaction with a CDI is contained within the contract, the company needs to verify that its practices meet the demands of the DOD Cyber Security program recommendations.
DOD Cyber Security Program Guidelines
Among the guidelines that the DOD suggests for contractors are:
- Security Standards: At a minimum, contractors should implement the National Institute of Standards and Technology Special Publication 800-171 (“NIST SP 800-171”). This implementation includes putting together a system security plan and an action plan. Both of these plans must be approved by DOD personnel.
- Rapid Incident Reporting: After an incident occurs, contractors have up to seventy-two (72) hours to submit a report. Reportable incidents have an expansive definition. All accounts must be made to the Defense Industrial Base (DIB) portal and require contractors to have a DOD-approved Medium Assurance Certificate. Because of how tiny the reporting window is, contractors should apply for this certificate in advance.
- Cloud Computing Standards: The DOD Cyber Security program has its own recommendations for cloud-based solutions. If the business has its own in-house cloud solution, it must implement the NIST SP 800-171. For those using third-party cloud suppliers, the vendors must align with the Federal Risk and Authorization Management Program (“FedRAMP”) Moderate baseline. Vendors must also comply with all obligations related to forensic analysis, media preservation, malicious software, and incident reporting, and damage assessment.
Relying On Your Business Practices
Contractors already have their own standards for operation regarding their cybersecurity departments. However, it doesn’t hurt to have a fallback position. Sync Resource has an understanding of the NIST cybersecurity framework that both the CMMC and the standard DOD cyber security program obligations require. If you’d like a third-party audit of your systems or just advice on how to improve them, give us a call. We’ll be glad to ensure that you’re fully compliant with the DOD Cyber Security standards.